Cryptojacking Meets IoT
Hackers can now break into your security cameras and use them to mine cryptocurrency. This week, LMG’s team released new research demonstrating that Internet of Things (IoT) devices are vulnerable to “cryptojacking.” In this post, we’ll show how we infected a popular security camera with the Mirai botnet, and used it to mine Monero coins.
“Cryptojacking” is the latest trend for criminals, who hijack your computers, install cryptocurrency miners, and use stolen information from your databases to set up wallets for illicit funds transfers. At the same time, hackers are busily infecting the Internet of Things. By 2020, researchers estimate there will be 30 billion IoT devices in the world. Many of these devices are highly vulnerable to simple attacks based on weak passwords and unpatched vulnerabilities, and poorly monitored— a perfect recipe for criminals to install mining software and lurk, racking up money.
What happens when cryptojacking meets the Internet of Things? LMG’s research team wanted to find out!
Step 1: Meet Our Victim
We purchased the #1 Best Seller in Hidden Cameras on Amazon: a TENVIS HD Wireless IP camera. According to the manufacturer, this baby has night vision with the fancy “Smart Eyes” technology. It “helps protect your home from theft” and as a bonus, it’s completely hackable!

The security camera runs a version of embedded Linux on a GK7102 chip. It has a 600 MHz ARM CPU and 512 MB of RAM.
Step 2: Vulnerability Test
Can we break into the camera? We hooked it up to a wireless network in LMG’s “Play Lab,” and ran a port scan using Nmap. As you can see from the results below, the camera is running Telnet, as well as two web servers, and audio/video streams:

Next, we ran the “ncrack” brute-force password guessing utility, using the password list included with the Mirai IoT botnet distribution. In just a few seconds, it successfully guessed the camera’s root password (00000000). Very tricky!
Step 3: Set Up the Botnet
We opted to use the Mirai IoT botnet for our proof-of-concept hack. Mirai is designed to hack into common IoT devices by leveraging weak or default credentials. Mirai burst into the public spotlight in 2016, when attackers used it to hack hundreds of thousands of devices and launch a massive DDoS attack that took down Dyn, a major DNS provider. The Mirai source code is publicly available, making it a perfect candidate for our proof-of-concept experiment.
Mirai includes two components: the client software used to configure and manage the botnet, and the command-and-control (C&C) server that communicates with the infected bots. We set both of these up in the virtual lab environment.
Step 4: Mining Software
We chose to use the Minerd cryptocurrency mining software, because it is lightweight, has a small list of dependencies, and there’s a version specifically tailored to ARM processors.
At LMG, we handle lots of forensics cases involving cryptojacking. In the vast majority of cases, the hacked systems are set up to mine Monero (XMR) because you can mine Monero using commodity hardware, unlike other cryptocurrencies like Bitcoin.
We set up our wallet at My Monero. This was a very quick process, as advertised:
Step 5: Modifying Mirai
Mirai includes a variety of modules that execute attacks (primarily Denial-of-Service). These include SYN floods, UDP floods, and more.
We added a new module designed to retrieve and run a shell script from the C&C server. This shell script retrieves, loads, and executes everything needed for the “minerd” cryptocurrency mining software to run. You can see the new module in the screenshot below:

Step 6: Initial Pwnage
Using our special modified version of Mirai, we launched our attack at the camera’s IP address (192.168.2.220). Mirai guessed the camera’s password and logged in via Telnet. As shown in the screenshot below, Mirai forced the camera to make an HTTP GET request to the C&C server, in order to download Mirai’s initial installation script (bins.sh).
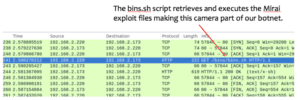
The bins.sh script retrieves and executes the Mirai exploit files with the assistance of the camera’s built in “dvrHelper” utility, making this camera part of our botnet. The IP address and credentials for the camera are also stored in a list on the server so we can re-infect the camera if it is rebooted or reset.
Step 7: Heartbeat
Below you can see a network flow graph generated by Wireshark. This shows the “heartbeat” communication between the infected device and the server. Communications occur roughly every 60 seconds. This is how the camera checks for orders. In our version, the botnet can DDoS a server or mine Monero using the Minergate XMR mining pools. Our Monero can then be anonymously transferred to our shiny new My Monero wallet from the Minergate web portal.
The Mirai botnet uses port 23 (Telnet) to communicate with infected devices. The good news for security pros is that this is easy to spot and block on your network. As you can see, it doesn’t actually use the Telnet protocol; it simply exchanges raw data over port 23 (TCP).

Step 8: Start Mining!
Using our new Mirai module, we sent the camera an instructing to commence cryptocurrency mining! This caused the camera to retrieve our script, “not_a_miner.sh,” from the C&C server, as shown in the figure below. The script builds and executes a stripped-down version of the minerd software, and configures it to use our shiny new wallet.
Once the minerd software is up and running, you can see that the camera communicates extensively with the Minergate XMR mining pool. Again, this should be easy for defenders to catch and block using network monitoring software.
Step 9: Hard at Work
Our little camera was now working hard to make us some big money!! As you can see, the CPU was pegged at 200%.
The camera was really straining, too. After a few hours, it malfunctioned and started making a sad little cry:
Cryptojacking may not be as dramatic as ransomware, but it can certainly impact the lifespan and functionality of your equipment— often in ways that are difficult to diagnose.
Once the camera was rebooted, Mirai easily reinfected it and it went right back to work.
Step 10: Sit Back and Roll in the Dough
When we checked in a day later, we were rich! OK, not quite. We had made .000054414035 Monero (almost a penny!)
Maybe cybercriminals will set their sights on bigger prizes— beefier cameras, fancy HVAC systems, etc. Or perhaps they’ll just go for volume and time. If you hack 20,000 cheap security cameras and make a penny a day from each, that’s $200/day, or $73,000/year. Not bad.
Conclusion:
LMG’s proof-of-concept project demonstrated that launching a cryptojacking attack against a common IoT device is not only effective; it’s easy. Using widely available IoT botnet and cryptocurrency mining software, attackers can infect vulnerable devices en masse and use them to generate recurring revenue. This means criminals now have strong, direct financial incentives to infect as many IoT devices as they can.
The biggest risk to IoT hacking is performance and physical damage. For example, when an attacker installs a cryptominer on a device, they are using processing power. The cryptomining software can easily overload the device. Imagine if your building HVAC system suddenly stopped working, because a cryptominer used up too much of its computing power. At LMG, our forensics team has even seen cases where a cryptominer caused a device to overheat and catch on fire. That can destroy very expensive equipment if you’re unlucky.
The solutions are simple:
• Keep track of your IoT devices. Make sure to involve your IT team right at the procurement phase, so they can be involved in device selection and provide guidance on security.
• Change the passwords so they are not the default.
• Patch IoT software regularly, just like workstations and servers.
• Place devices behind firewalls and only allow access on an as-needed basis.
• Block any unnecessary traffic to or from your devices.
• Monitor your devices’ network activity and respond to suspicious behavior.
Thanks for reading, and follow @LMGSecurity on Twitter for future updates!
/* This research project was conducted by Matt Durrin and Sherri Davidoff, with contributions from LMG Security team members Karen Sprenger and Ali Sawyer. Many thanks to the LMG Security team for all of their excellent work on this project. */

