All hackers need is the tiniest foothold inside your network, and they can take over, stealing your most valuable data, launching ransomware attacks, and more. Watch as we demonstrate a full real-world takeover, starting with zero access from the Internet. Learn how to thwart hackers with simple configuration changes and strong auditing techniques.
Hackers exploit human vulnerabilities in order to divert funds, break into your cloud, install malware and more. Watch the latest attack trends and techniques in this fast-paced webinar.
Criminals are targeting cloud apps and infrastructure, stealing loads of sensitive information and holding companies hostage. How do attackers break in, and what exactly do they do with access when they have it? In this fast-paced talk, we’ll show you how hackers:
- Hijack API keys and Break into your cloud infrastructure
- Exploit common misconfigurations to scrape data and compromise applications
- Spread from on-prem to the cloud (and vice versa)
- Lurk in your systems to steal data, hijack payments, and more
- Hold your cloud data hostage unless you pay a ransom
Along the way, we’ll also show you tips and tricks on securing your cloud infrastructure and locking hackers out before they get their hands on your goldmine of data.
What are the hottest issues in cybersecurity right now? We’ll discuss new exploits and cutting-edge security research from the 2023 Black Hat and DEFCON conferences in this fast-paced webinar. We’ll also share the conference highlights, what they mean for you, and what your organization can do to defend itself against an increasingly complex and dangerous digital landscape.
What makes the dark web so dark? Join us for a deep dive into the inner workings of the darkest corners of the internet. Come along for a guided tour of the criminal underground and see first-hand how hackers and criminals use the anonymity of the dark web to sell their goods and hide their crimes. We’ll also cover how the dark web can be used for good by enabling spies, journalists, and others to protect their privacy. Finally, we’ll discuss how the dark web and the underground economy it provides are directly related to the latest cyber threats, enabling hackers to buy malware, 0-day exploits, and much more.
Cybercrime has evolved rapidly, and we all need to hone our response techniques to match. Today’s adversaries are increasingly destructive and have developed effective techniques for rapidly destroying your IT infrastructure. During the aftermath of an attack, they routinely monitor the victim’s communications and may even conduct social engineering attacks based on your incident response processes. Join us and get practical strategies for adapting your incident response best practices to reflect today’s increasingly interconnected threat landscape.
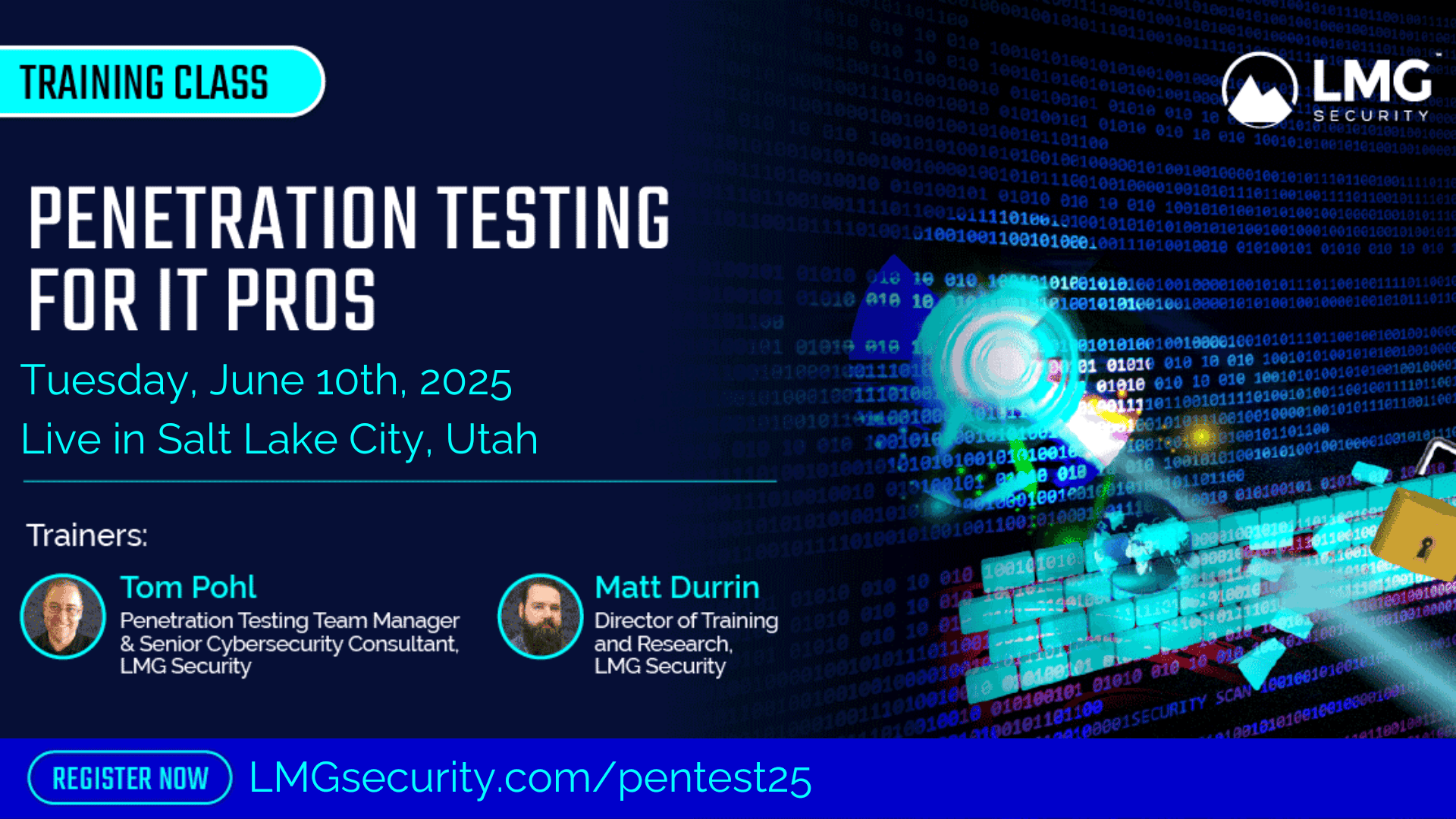
Join Marco and LMG Security for an event on Printer Security on Thursday, June 8th at Court Avenue Brewing. We are excited to have Tom Pohl, Penetration Testing Team Manager and Senior Cybersecurity Consultant from LMG Security, demonstrate hacking.
With the growing trend of Bring Your Own Device (BYOD) to work, the risk of mobile device security breaches is increasing rapidly. In this fast-paced webinar, we’ll cover the key threats to mobile device security, common gaps in BYOD policies, and how you can protect your organization’s sensitive data on the go.
Not all security technologies are created equal! Get the inside scoop on which security controls are the most effective and what to prioritize. We’ll walk through real-world cases, discuss underlying factors and highlight solutions that really work.
Often on penetration tests we encounter printers. Lots of printers. Come watch as we demonstrate how to make your printer do things that will make your IT admins gasp in fear! Along the way, we’ll provide tips for stopping hackers at every stage.
Your organization’s security is only as strong as its weakest link – and that link could be your vendors. From Rackspace to Okta to MSP hacks and more, discover how technology vendors, software providers and other suppliers can leave you vulnerable to cyberattacks.
Ransomware has gotten sneakier. In response to highly-publicized law enforcement busts and disruptive measures, criminals have developed novel tactics such as partial encryption strategies, which are designed to speed destruction and evade detection. In this fast-paced talk, the authors of the new book, “Ransomware and Cyber Extortion,” will demonstrate the latest techniques and provide critical guidance for protecting your organization.
All hackers need is the tiniest foothold inside your network, and they can take over, stealing your most valuable data, launching ransomware attacks, and more. Watch as we demonstrate a full real-world takeover, starting with zero access from the Internet. Along the way, we’ll provide you with tips for stopping hackers at every stage.
Cybercriminals want to break into your email to steal sensitive data, conduct fraud, or reset passwords for your other accounts. In this webinar on November 9th, we’ll show you how hackers break into your email, fake invoices and wire fraud examples, how to recognize spoofed emails, and the top ways to protect your email account.